Advantages of building secure realtime applications with Pusher Channels
In the digital age, realtime applications powered by technologies like WebSockets are pivotal for dynamic user interactions. Explore how Pusher Channels simplifies the challenge of building secure, interactive apps.
Introduction
In the era of digital transformation, realtime applications have become a necessity for providing an interactive user experience. Realtime technologies like WebSockets have revolutionized the way we build interactive applications by enabling bi-directional communication between the client and server.
However, developing secure realtime applications can be challenging. In this post, we'll explore how Pusher Channels can help developers overcome these challenges and build secure realtime applications.
Security concerns in realtime applications
Security is a critical concern when developing realtime applications. The nature of these applications, which often involve constant data exchange between servers and clients, can expose them to various security threats.
1 - Data security
Data security is crucial for realtime applications as they frequently handle sensitive information that needs to be protected from unauthorized access and data breaches. If you are a developer working on such an app, you’ll want to look to implement encryption, secure key management, and data integrity checks.
Pusher Channels uses secure WebSockets (WSS) by default, providing encrypted data transmission between clients and servers. It also provides the ability to use Private, Encrypted, and Presence channels, which can enhance data security by restricting who can access certain data as well as encrypting the data.
2 - Authentication and authorization
You need to make sure the apps you develop accurately authenticate users to prevent unauthorized access. This includes implementing multi-factor authentication, proper session management, and ensuring that authorization checks are carried out on the server side.
With Private, Presence, and Encrypted channels, authorization is required. Clients must be authorized by your server before they can subscribe to these channels. The process of authorizing a user can be as simple or as complex as your application requires, allowing for various levels of security.
If all connections to your app either undergo authorization by subscribing to a private/presence channel or proceed through user authentication, then the "authorized connections" feature can be activated. This setting instructs Pusher to automatically terminate any connections to your app that fail to complete the authorization or authentication process within a 30-second window. Not only does this provide an added layer against unauthorized access, but it also ensures that such unauthorized connections don't contribute to your concurrent connection count. For more details, refer to Authorized connections.
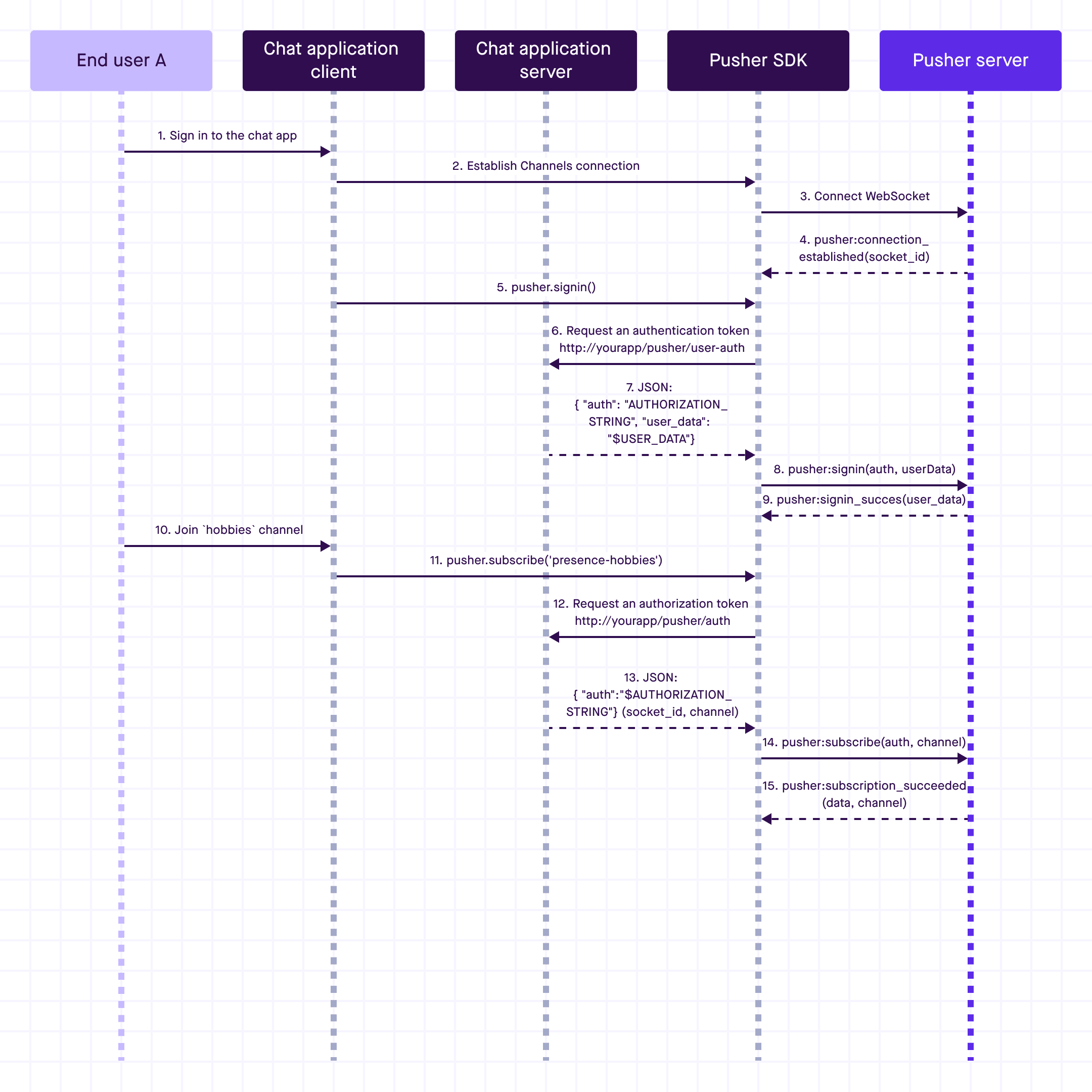
When using the user authentication feature in Pusher Channels, you have another feature at your disposal—terminating user connections. If you've got a user causing trouble and you want to boot them out of your app, you can use the Pusher server SDK to cut off all their active connections. But remember, this only cuts off their current connections. They can still reconnect unless you also prevent or reject future authentication attempts.
3 - Realtime data streaming security
If you are using protocols such as WebSockets for live data transmission when developing realtime applications, your connections must be secured (for example, using WSS or HTTPS), and care must be taken to prevent issues like data leakage and replay attacks.
This is a good opportunity to mention the forceTLS flag in Pusher client libraries. This flag allows you to ensure connections are only made using encrypted protocols such as WSS/HTTPS.
4 - Scalability and performance
Realtime applications often need to handle a high volume of concurrent connections and data streams, and must do so without sacrificing security. Developers must carefully manage resources and implement robust rate-limiting and load balancing strategies.
Delivering a realtime experience at scale is tough. Holding an open connection between your service and a client over a WebSocket is relatively easy, but as you scale from one device to thousands or even millions, you not only have to keep these connections open, but you need to deliver a throughput of millions of messages per second.
Pusher Channels takes care of the scalability and performance issues associated with realtime applications. It allows you to focus on building your application without worrying about how to handle a high volume of concurrent connections and data streams.
For example, Pusher introduced an event type called Subscription Count event. This event automatically provides the number of connections currently subscribed to any given channel, which allows developers to implement presence at scale.
This feature is particularly useful for developers who are building realtime applications and want to overcome the scalability and performance challenge. It allows them to show a realtime count of thousands of live users in their app, which could be useful for showing audience size in a live stream, number of users waiting in a queue, or how many players are live in an open world game.
5 - Privacy
Depending on the region, developers may have to comply with data privacy regulations such as GDPR, HIPAA, or CCPA. This might require implementing features like data anonymization, user data access, and right to be forgotten.
For such scenarios, you will implement Encrypted channels. The application can include protected or sensitive information such as Protected Health Information in event payloads for private channels. As only your application manages the encryption keys, Pusher has no access to data included in encrypted events.
Because Pusher only handles the data for transmission, think of Pusher Channels with full encryption as a secure communication link. For more technical details, check out our blog post on how to achieve HIPAA compliance with Pusher Channels and here in the Pusher Support knowledge base.
6 - Infrastructure security
Developers can either build their own infrastructure for realtime features or choose an off-the-shelf API. Building your own may offer more flexibility but comes with challenges such as maintenance, security, reliability, tooling and analytics, as well as implications for the costs and time to market for your app. Hosted APIs offer a faster ready-made solution and take care of many of the operations associated with your infrastructure.
This includes securing the servers where the application is hosted, implementing firewalls, ensuring secure communication between different services, etc.
Luckily, with Pusher, you don’t have to worry about infrastructure at all. We take care of the data center and network security, access control, system security, and we get pen tested regularly. To minimize the downtime and data loss, we have disaster recovery and business continuity practices in place.
7 - Secure realtime APIs
Realtime APIs, like those provided by Pusher Channels, are crucial for enhancing the security of realtime applications. They allow developers to access and process data quickly, enabling faster responses to security incidents. If developers are polling an API for data changes, it indicates a need for a realtime API that pushes data to them instantly.
Certain data, such as safety notifications, are time-sensitive and require realtime APIs for immediate awareness of issues like process breaches. Realtime APIs are vital for systems monitoring, market data, communications, collaborative experiences, and realtime user experiences.
Securing realtime applications involves protecting API endpoints, securely managing API keys, and monitoring API usage for potential misuse. Pusher Channels enhances this security by using an app's API key, secret, and optional encryption key, all established when setting up the Pusher Channels app.
How Pusher Channels enhances realtime app security?
Here’s how to use Pusher Channels as a solution to enhance the security of realtime applications providing a safer and more reliable user experience.
- End-to-end encryption - One of the standout features of Pusher Channels is its support for end-to-end encryption. With this feature, sensitive data sent via Pusher Channels is encrypted in transit and can only be decrypted by the intended recipient. This prevents Pusher from reading sensitive content such as medical or financial data. The encryption is implemented on a new channel type, which begins with private-encrypted-. The encryption and decryption process is handled automatically by the Pusher library, making it easy for developers to implement.
- User authentication and authorization with the added value of terminating user connections. Now you can focus on building secure user-centric realtime apps.
- Authorized connections - Use this to ensure every connection to your channels app has been authenticated or authorized by your endpoints. Any connection that doesn't subscribe to at least one authorized channel will be disconnected after a timeout. Connections that are terminated in this manner do not count towards your connection count.
- Private channels - Pusher Channels allows you to publish sensitive data via private channels. Apps must get permission to subscribe to a private channel, providing an additional layer of security. For example, you can restrict a channel named private-user-alice so that only Alice's apps can subscribe to it.
- Presence channels - Presence channels show who is online, providing a way to track and control who is connected to your application. When a user's app subscribes to a presence channel, the app provides the user id, allowing other users' apps to see who is online. Here’s everything you need to know about Presence channels!
- Webhooks and API - You can activate webhooks in your account dashboard on a per-app basis. Pusher Channels provides webhooks and APIs that allow you to monitor your application's activity and to help you debug. This can be useful for detecting and responding to security incidents.
Best practices for secure realtime applications
While Pusher Channels provides the tools to secure your realtime applications, it's up to you to use them effectively. Here are some best practices to follow:
- Use Private and Presence channels - Whenever possible, use private and presence channels instead of public ones. This ensures that only authorized clients can subscribe to your channels.
- Secure both the authentication and authorization endpoint - Your authentication endpoint is a critical part of your application's security. Make sure it's only accessible over HTTPS and that it properly validates authentication requests.
- Monitor channel activity - Use Pusher webhooks to monitor activity on your channels and detect suspicious behavior. Consider setting up alerts for unusual activity, such as a sudden spike in subscriptions.
- Control access to your app - Anyone with your public app key can connect to your Channels app by design. This allows easy Channels use without needing the server-side authentication setup. However, publishing data in a production system over public channels isn't a recommended approach. Making use of private and presence channels, or user authentication, allows you to control what users and connections are able to receive published data. You can further protect against unauthorized access by enabling Authorized Connections.
Start building with Pusher
While realtime applications offer many benefits, they also present unique security challenges. Pusher Channels provides a robust set of features that can help developers build secure realtime applications.
Start building with Pusher and sign up for a free sandbox account!